The Red Team objective is to evaluate the effectiveness of a security plan. This is achieved through the emulation of behaviors and techniques of a potential attacker in the most realistic way possible.
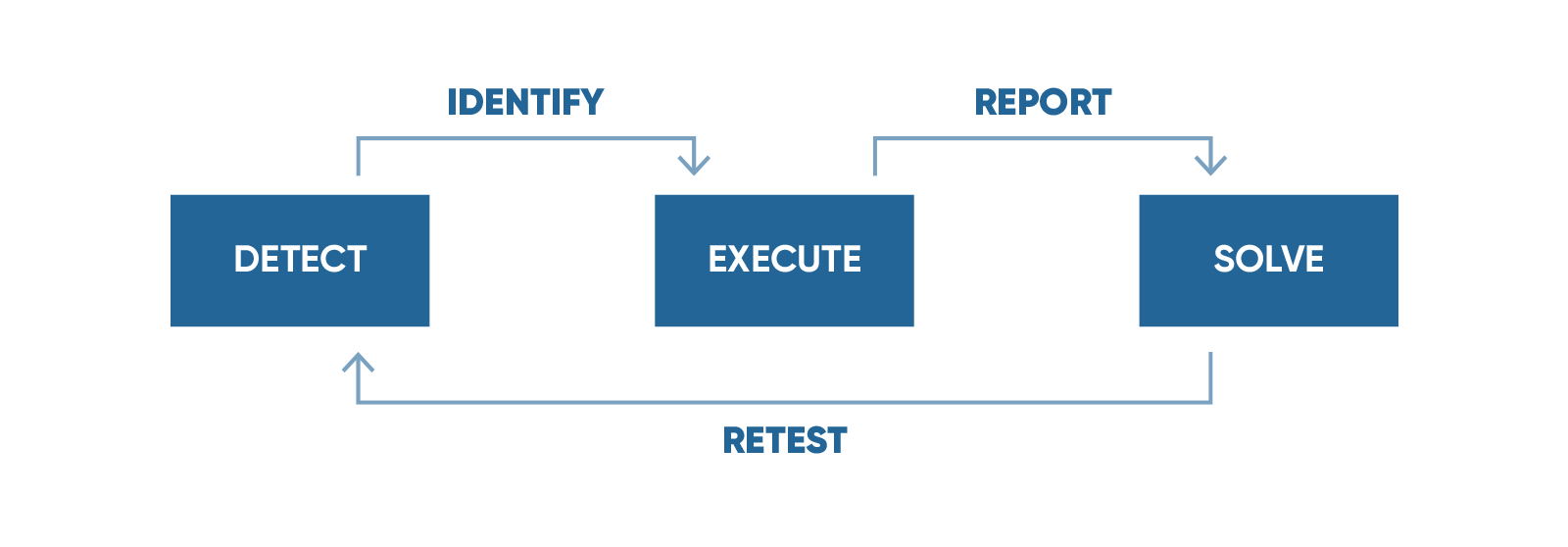
Detect
Your organization’s weak points and the best attack strategy.
Execute
The attack plan and find out your current protection status.
Solve
The issues and minimize your level of exposure.
the red team.
The Red Team objective is to evaluate the effectiveness of a security plan. This is achieved through the emulation of behaviors and techniques of a potential attacker in the most realistic way possible.
Red Team Operations represents the assembly and execution of a strategic plan, involving the infiltration to the physical and computer infrastructure of the target organization in order to obtain and exfiltrate an object, piece of data or specific asset and verify the effectiveness of preventive, detective, recuperative and resilience capacities of the organization.
Penetration Testing
Set of tests that emulate an attack from a malicious agent to find weaknesses and vulnerabilities in the structure of the organization.
Offensive Strategy
Long-term attack strategic plans allowing to work into the complete knowledge of the organization’s architecture and directly interacting with its blue teams.
Cyber Threat Intelligence
Deployment of 4 teams responsible for detecting, analyzing and documenting any attack, (either real or potential) that may threaten the organization. Its main purpose is to comprehend the external and internal real risks, define its effectiveness level, alert the organization, and establish the necessary countermeasures.
WE OFFER
Determination of the real risk level of your information and actives
Analysis of current attacks techniques, and the market’s motivations
Identification of configuration vulnerabilities and faults that may expose you
Mitigation of the weak points, before an attacker can exploit them
Testing of your protection and detection systems
Preparation of the organization for strategic changes
THE MKIT SIGNATURE
FAQ
What is the difference between Red Team Operations and Penetration Testing?
Red Team Operations involve the execution of different offensive tasks, including different areas (computer, physical, human) at the same time with a single specific objective planned. Once the objective is reached, the operation concludes and the project ends.
Penetration Testing represents the massive and general search for vulnerabilities, with the final objective of identifying and verifying as many of them as possible in order to test them and report them, thus establishing the general security level of the environment, application or specific group being analyzed.
Red Team Operations execution generally includes the execution of Penetration Testing tasks, although it may not be limited to it.What is a “Purple Team”?
The Purple Team exists to ensure and maximize the effectiveness level of both Red and Blue Teams. This is accomplished through the integration of defensive and control tactics by the Blue Team with the threats and vulnerabilities found by the Red Team in a unique instance that guarantees that the efforts of both teams are being leveraged at the maximum.
In an ideal situation, the Red Team creates challenges for the Blue Team to solve. In doing so, both teams together are able to improve the organization security level and enhance the skills of all the people involved in the project.
Through the implementation of a Purple Team solution, a strong synergy is accomplished that delivers added value to the end result.What is the difference between an automated and a manual analysis?
The automated analysis tends to be faster and simpler, but their reach is limited. It is based solely on the execution of Software and/or Hardware tools with preloaded profiles, that perform a general diagnostic, without depth or customization.
The manual analysis adds an extra level in depth and customization by involving specific, thorough research processes in its entirety without using tools, but with manual evaluation techniques. This way the experience, creativity, and the innovation potential of each resource is evidenced in the quality of the delivery.
Manual analysis generally include the execution of automated analysis, but only as initial and general steps, not as the main execution plan. When the automated analysis ends, the Mkit team will continue analyzing manually, based on the current market research as well as their own, to achieve a more specific and precise result.
Manual analysis is the best method to suppress most of the false positives/negatives, delivering a more concise and more solid final report.
You should hire a Red Team if you need to identify vulnerabilities in your infrastructure and systems, and test your security controls. A Red Team allows a fresh set of eyes to take a look at your overall status.


