A Blue Team consists of a security team that strategically defends the organization against real attackers or even Red Teams.
Identify
Faults on actives and processes, and your potential attack vectors.
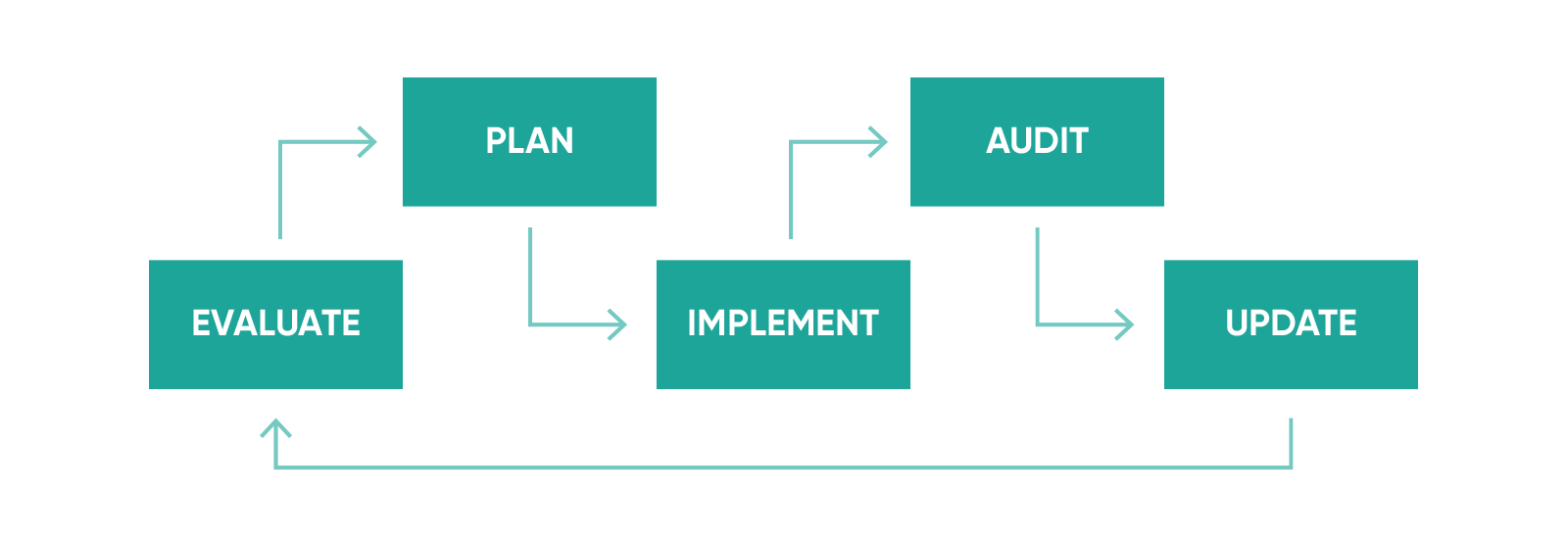
Evaluate
The organization general risk and its current protection level.
Implement
A plan according to the specific requirements of the situation.
the blue team.
A Blue Team periodically analyzes the effectiveness of the security policies and measurements taken by the organization, to ensure that all potential risks and threats are being revised, identified and mitigated.
The Blue Teams differ from the standard security teams in the sense that they possess the conscience of constant surveillance before attacks, being this the mission and main perspective of a true Blue Team.
The execution of Blue Team projects is carried out inside a macro project, with a bigger focus that covers both offensive and defensive techniques, inside a long-term execution plan.
MANAGED SERVICES
Planification and execution of company-wide security subprojects, with both defensive and offensive techniques, within a strategic general scenario.
Application Security
Protection techniques for application development, from the design period to their set on production and continuous maintenance.
Training
Corporate strategic training through hands-on, high-technical content courses, developed on-demand according to the needs of each specific case.
WE OFFER
Creation of a long term defense strategy
Strengthening of current security processes
Establishment of a maturation measurement Baseline
Increase in the level of reliability of the organization’s general protection
Training to employees on the latest threats and countermeasures
Preparation of the organization for higher level and criticality responsibilities
THE MKIT SIGNATURE
FAQ
What is a “Purple Team”?
The Purple Team exists to ensure and maximize the effectiveness level of both Red and Blue Teams. This is accomplished through the integration of defensive and control tactics by the Blue Team with the threats and vulnerabilities found by the Red Team in a unique instance that guarantees that the efforts of both teams are being leveraged at the maximum.
In an ideal situation, the Red Team creates challenges for the Blue Team to solve. In doing so, both teams together are able to improve the organization security level and enhance the skills of all the people involved in the project.
Through the implementation of a Purple Team solution, a strong synergy is accomplished that delivers added value to the end result.Is hiring a Blue Team truly necessary?
No. The internal security team and IT and development departments can perform the healing tasks that the Blue Team does. They would be able to understand the reports presented by a Red Team and make the necessary updates to mitigate any risks. With a Blue Team, tasks can be more robust to strategically plan the organization growth, but it isn’t vital to arrive at an acceptable security status.Why is it important to start developing security processes at the planning stage?
The anticipated addition of the security processes to the development life cycle allows to ensure that the protection activities (architecture analysis, code review, penetration testing) are applied parallel to the development process, enabling a direct interaction between the teams. This synergy creates a robustness in the code that is impossible to achieve by any other means, while saving the organization both time and money.
Blue Teams work from the inside out. They have access to all the necessary documentation and systems and actively participate in management meetings to contribute ideas relating to the security strategy.


